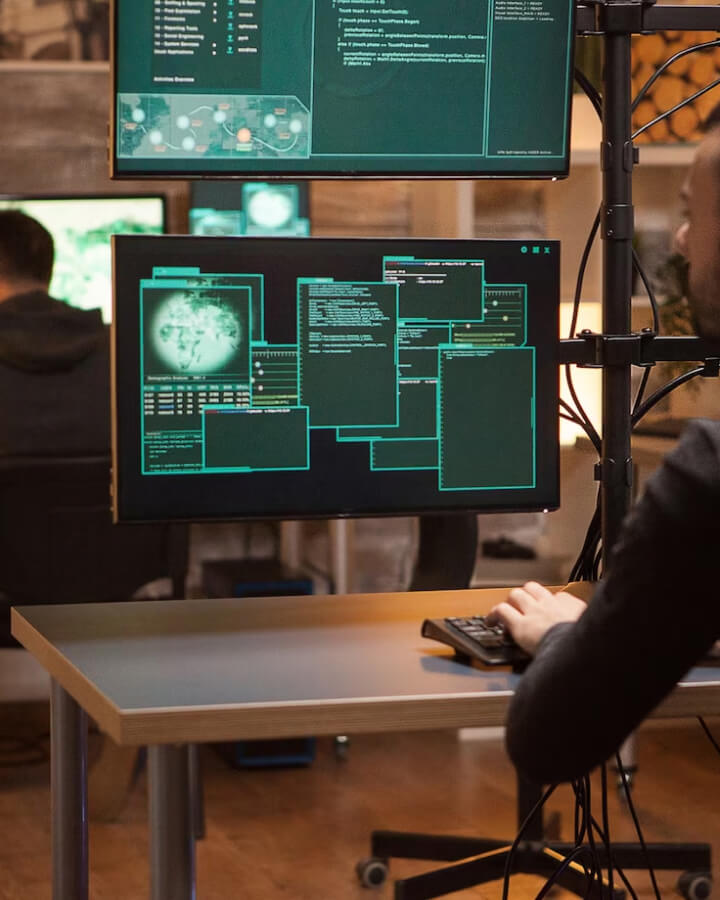
Security project design
Attaining the most effective security solutions entails a vigilant process in tracking technological advancements in integrated protection and communication technologies. It also involves skillfully tailoring protection solutions to meet the specific preferences and genuine needs of users.